Prerequisites
Before you begin, you need:-
To register your application with Auth0.
- Select an appropriate Application Type.
- Add an Allowed Callback URL of
{https://yourApp/callback}. - Make sure your application’s Grant Types include the appropriate flows.
- A valid Google Workspace account and your own Google Workspace organization.
- Administrator privileges on the Google Workspace organization.
Register your application with Google
To allow users to log in using Google Workspace, you must register your application in the Google Cloud console. Follow Google’s Setting up OAuth 2.0 doc and use the following settings:-
On the consent screen, under Authorized domains, add
auth0.com. -
When asked to select an application type, choose Web application and set the following parameters:
Unless you’re using a custom domain, your tenant’s domain name is
Field Description Name The name of your application. Authorized JavaScript origins https://{yourDomain}Authorized redirect URIs https://{yourDomain}/login/callback<TENANT NAME>.<REGIONAL SUBDOMAIN>.auth0.com. For example, the domain name of a US region tenant namedexample-nameisexample-name.us.auth0.com). Tenants created before June 2020 omit the regional subdomain. - If you plan to connect to Google Workspace enterprise domains, you need to enable the Admin SDK API.
Configure a Google Workspace enterprise connection in Auth0
Create a Google Workspace enterprise connection
From Auth0 Dashboard > Authentication > Enterprise, find Google Workspace and select Create.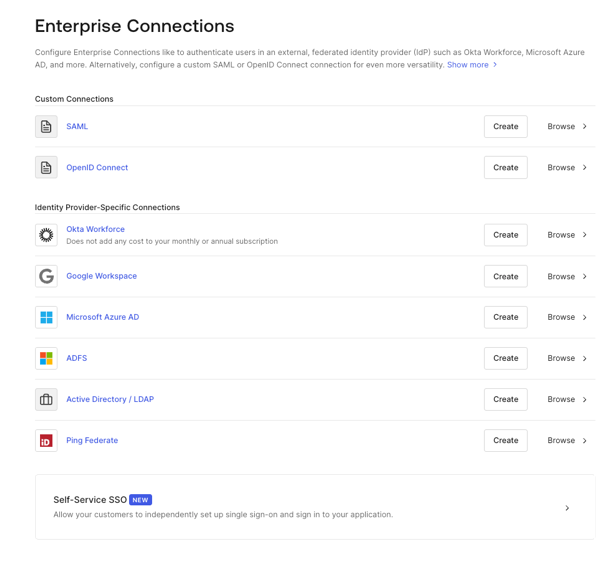
Choose your connection's configuration settings
On the creation page for a new Google Workspace enterprise connection, configure its settings:
When you finish choosing your settings, click Create.
| Field | Description |
|---|---|
| Purpose | The use for the connection: login, connected accounts, or both. To learn more, read User authentication vs Connected Accounts. |
| Connection name | A logical identifier for your connection. It must be unique for your tenant and cannot be changed. |
| Google Workspace Domain | The Google Workspace domain name for your organization. |
| Client ID | A unique identifier for your registered Google application. Enter the client ID for the app you registered in the Google Cloud console. |
| Client Secret | A string used to access your registered Google application. Enter the client secret for the app you registered in the Google Cloud console. |
| Attributes | The attributes of the signed-in user that your app can access and that Auth0 stores in the user profile:
|
| Extended Attributes (optional) | Additional attributes for the signed-in user that your app can access and that Auth0 stores in the user profile:
|
| Enable Users API (optional) | Enabling this setting allows the connection to make calls to the Google Directory API. |
| Auth0 User ID (optional) | By default, the Auth0 user_id maps to email. By enabling Use ID instead of Email for Auth0 User ID, user_id instead maps to id. You can only set this for new connections and cannot change it once configured. |
Configure how users log in
On the Login Experience tab, configure how users log in with this connection:
After entering your settings, click Save.
| Field | Description |
|---|---|
| Home Realm Discovery | Compares a user’s email domain with the provided Identity Provider domains. For more information, read Configure Identifier First Authentication |
| Connection button | Check Display connection as a button to enable a button on the application login page for this connection. When you do, you can customize two options:
|
Verify Google administrator consent
On the Setup tab, either:
- Follow the Continue link if you have admin permissions to configure your Google Workspace settings to use Google’s Admin APIs, or
- Provide the given URL to your administrator so that they can adjust the required settings
Enable and test the connection
Enable the connection for your Auth0 applications, then test the connection to verify it works.
Next steps
Customize or automate user profile synchronization
On the Provisioning tab of the connection, you can configure how user profiles are updated:- Enable Sync User Profile Attributes at Login to allow Google to sync user profiles when the user logs in. When enabled, you can choose the Sync Frequency. By default, Auth0 refreshes user profiles on each login. You can also choose to sync on first login only.
- Enable Provision Users and Groups Using Directory Sync to automatically sync users and groups from Google Workspace to Auth0. To learn more, read Sync Google Workspace Users to Auth0 with Google Directory Sync.
Get access and refresh tokens
After a user authenticates, Google issues an access token. You can use this access token to call Google’s APIs. To additionally request a from Google, addaccess_type=offline&approval_prompt=force to the authorization request.
For Google Workspace, Auth0 stores access and refresh tokens in the user object for individual users and in the connection object for workspace admins. You can access them using the Management API’s Get a connection endpoint.
Retrieve additional user and group details
To retrieve additional user and group details beyond what Auth0 retrieves by default, you can use Google’s Directory Admin API to get a user’s extended group properties.- On the Settings tab of your enterprise connection, in the General section, under Extended Attributes, enable the Groups.
- On the Setup tab, complete administrator consent using the provided link.
-
Retrieve the admin access token stored in the
connectionobject using the Management API’s Get a connection endpoint. -
Use the access token to call Google’s Manage Groups endpoint. For example:
Validate authentication with Actions
Validating that authentication events are from legitimate users who are members of your Google organization can help prevent unauthorized access to your applications by users who are no longer part of your organization. To verify Google authentications, you can use a post-login Action to validate that theidp_tenant_domain claim associated with the user matches the expected organization. For example:
Example post-login Action code to validate Google authentications
idp_tenant_domain for users who authenticate with the following connection types:
- Google Social
- Google Workspace
- Google OIDC
More information
- Read more about the authentication flow
- Pass additional parameters to the identity provider
- Re-prompt users for permissions
Limits
- If you have an existing Google social connection for your application and you create a new Google Workspace enterprise connection for the same domain, users affiliated with the social connection will be logged in with the enterprise connection (even if you don’t enable it).
- The Google Workspace enterprise connection allows Auth0 user profiles to have up to 200 groups. If a user profile has more than 200 groups, these results may not be shown. If you use Google groups for authorization, you must secure the workspace to prevent unauthorized users from modifying groups.
- The connection button is not available for Classic Login. To enable and customize the connection button, use Universal Login.

